II. Hours vs. Days
The growth engine of modern asset backed finance is forward flow, programmatic capital commitments that buy receivables, consumer loans, and merchant advances every day. These commitments scale because the operating surface is tight. One platform. One warehouse line. Fast decisioning. Digital identity at application. Daily purchasing works when the asset is normalized at creation and the lender has continuous sight into performance. The same model was then carried into enterprise receivables without rebuilding the control layer. That is where the gap opened.
Forward flow was not the problem. Fast origination paired with slow verification was the problem.
High velocity worked when the system was closed.
Consumer forward flow proved speed under a coherent stack.
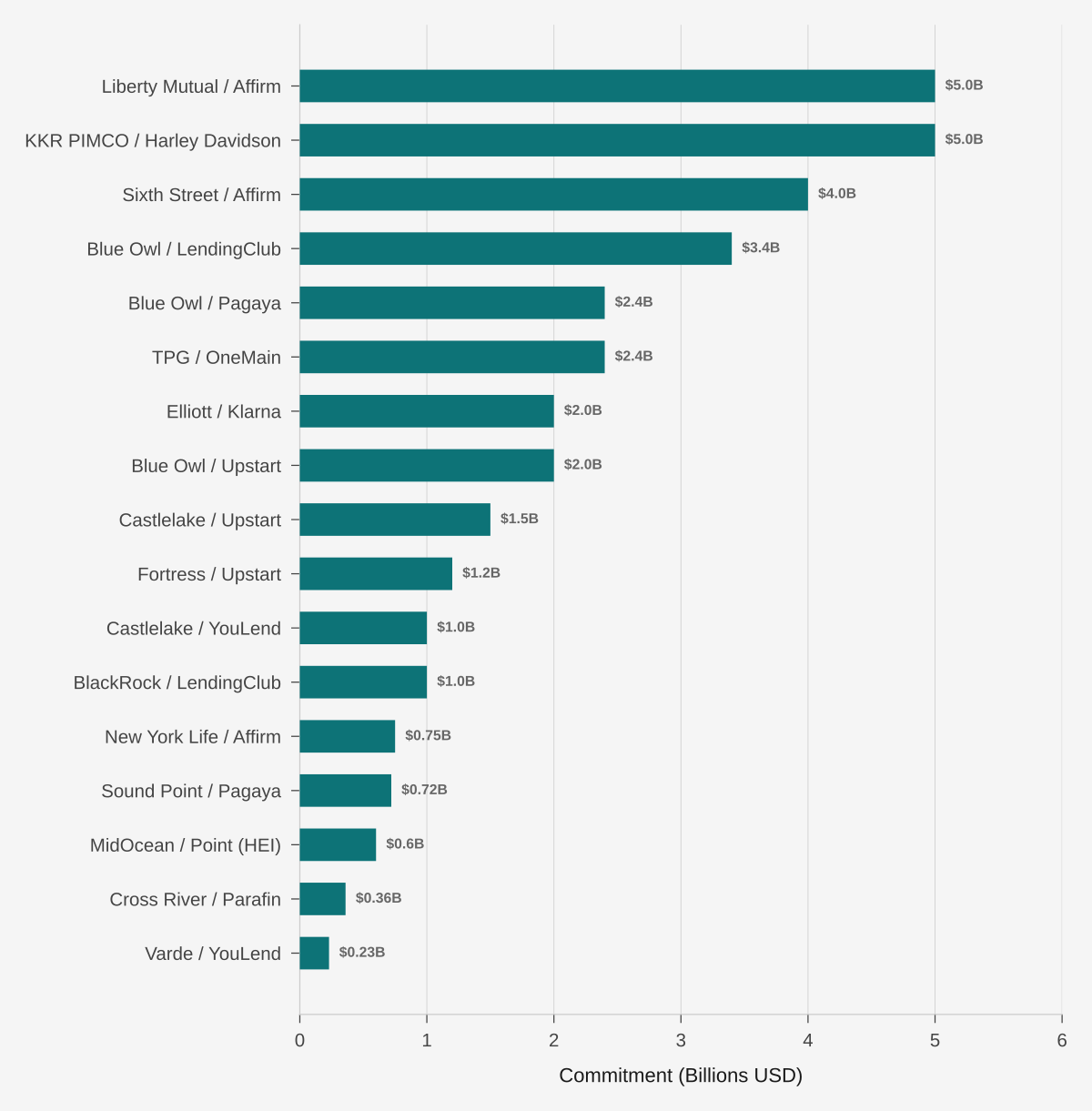
Consumer forward flow already proved that institutional capital will fund machine speed origination when the operational stack is coherent. Large commitments, Liberty Mutual and Affirm, KKR PIMCO and Harley Davidson, Sixth Street and Affirm, Blue Owl and LendingClub, all sit on cleaner identity, cleaner servicing, and tighter warehouse structure. Double pledge risk is structurally harder when one platform originates, one lender funds, and one system of record governs the asset.
The lesson is not that speed is dangerous. The lesson is that speed without shared verification is dangerous.
Sources: company announcements, press releases, PitchBook.
The fraud happened in the time delta.
Enterprise receivables kept the speed and lost the closed loop.
Enterprise receivables kept the speed and lost the closed loop. Assets could be purchased in hours while control infrastructure still refreshed on weekly, monthly, or quarterly cycles. Borrowing base certificates and field exams were designed for slower markets. A duplicate invoice submitted to two capital providers a few days apart could clear both portfolios before either review cycle ran. That is why the failure mode repeated across cases. The fraud did not beat the controls. It passed through the space the controls left open.
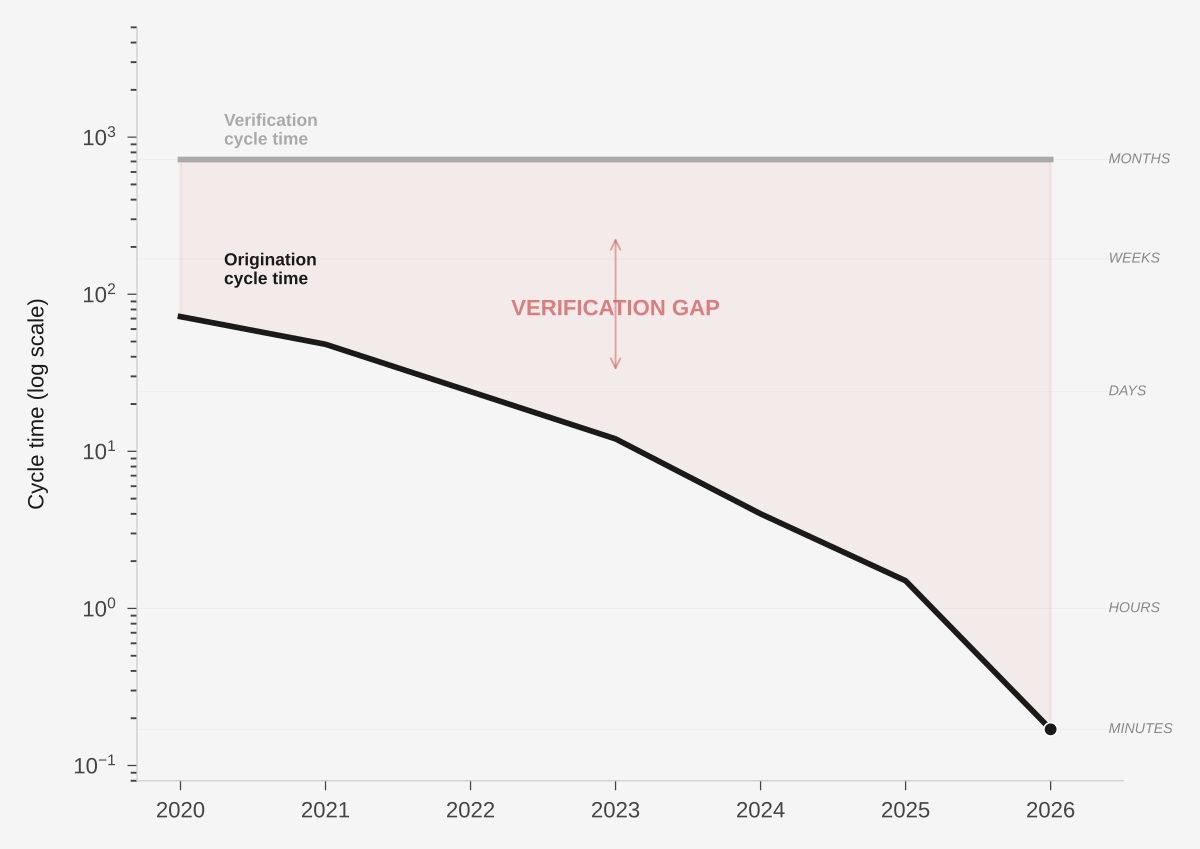
When origination runs at hours and verification runs at days or months, the attack surface is temporal before it is legal.
Sources: industry practice, MINT architecture.